The measures we take so our cloud-based solution provides complete protection for your organization’s content.

Our team trains and adhere proper Code of Conduct, network and operating system security measures. Learn more.
Organizations are working with higher volumes of data than ever before. And whether to ensure information is safe from an external data breach or that only designated team members can access confidential material, having proper security measures in place for your data is an important precaution that cannot be overstated.
We at Collabware understand how critical proper data privacy and security is. So today, we’re sharing the steps we take and extra methods we implement to ensure that any material stored in our cloud-based solution, Collabspace, is safe and secure.
What is Collabspace? Collabspace is a highly scalable, cloud-based information archive, discovery and management solution. We also refer to it as our data lake solution, as it enables organizations to stream in content from multiple platforms into one secure data repository. Depending on your organization's needs, you can select one of the Collabspace products for the purposes of archiving and data backup, advanced search, managing content lifecycle and/or extracting new value and insights from your data.
12 Safety Measures Offering Complete Content Security in Collabspace
If you are conducting a Privacy Impact Assessment to confirm that you comply with FOIPPA or just performing an internal check-in to confirm your organizational data is safe, we've highlighted 12 security measures we take so you can feel secure storing and managing your content with Collabspace. For the full, in-depth listing, you can also download our Collabspace Security Features brochure below.
1. Building with Safety and Compliance in Mind
A secure solution starts from the ground up, so we keep security and data privacy in mind as we build.
During Collabspace software development, our team not only follows best practices to address software and application security concerns, but takes extra steps to implement process controls. Access control and credential management is maintained during deployment and operations of Collabware application platforms.
Only code vetted by Collabware’s own QA process is promoted to the production environment, and only code built with Collabware’s build system can be deployed to our infrastructure. No ad-hoc code from unqualified sources is allowed.
Collabspace also invests heavily into product innovation and advancing EDRMS practices to highly-regulated standards such as FedRAMP High and SOC 2.
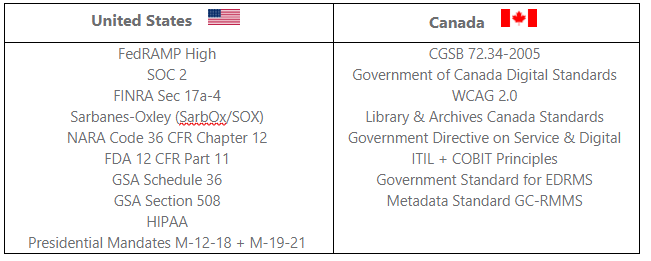
Our products undergo continual testing to remain accredited to these international records management and security standards. See our full list of certifications here.
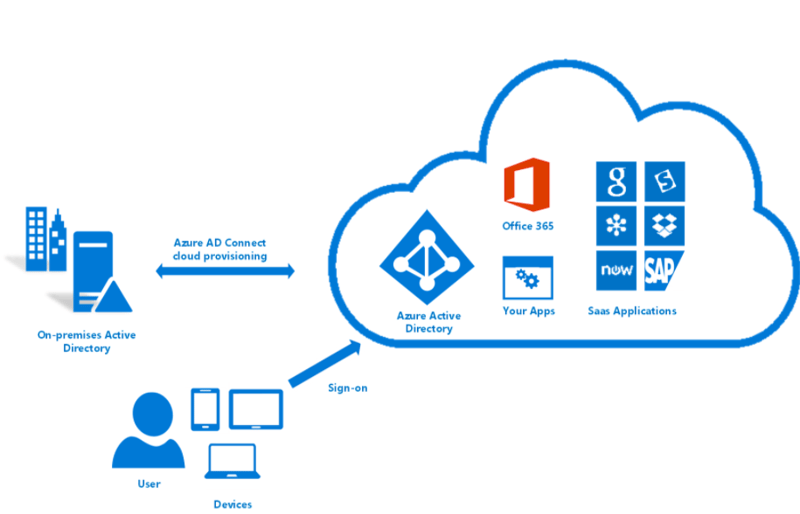
2. Leveraging the Security Strengths of Microsoft Azure
When we say we take building a secure solution seriously, we mean it. We’ve selected Microsoft Azure as our foundation for its proven security-backed benefits.
Collabspace is built on top of Microsoft Azure, with all data stored in Microsoft Azure data centers. These cloud environments meet demands of FedRAMP, the US government’s most rigorous security compliance framework. Integration with Microsoft Azure provides the following security measures:
- All source code is centrally stored in a cloud repository secured by Azure AD and can only be accessed by Collabware company-assigned computers (see Step 3).
- Azure KeyVault is leveraged to encrypt customer data (see Step 5).
- All data is stored securely in Microsoft Azure data centers (see Step 6).
- Full integration with Azure Active Directory for stringent authentication and authorization controls (see Step 8).
- Azure alerts and security reporting are leveraged to assist in identifying potential vulnerabilities for maximum Platform Operational security (see Step 12).
Microsoft Azure Active Directory, Image Courtesy of Microsoft.
3. Securing Source Code and Meticulous System Updates
All source code is centrally stored in a cloud repository secured by Azure AD and can only be accessed by Collabware company assigned computers. This is purely for the purpose of system maintenance. No Collabware staff have any access to any content stored within Collabspace, unless particular permissions are expressly given for certain individuals by the administrator on the customer side. All software and configuration changes to the Collabspace platform are run through a rigorous QA (Quality Assurance) process in multiple test environments to identify any issues prior to a production release.
In addition, the Product Operations team actively reviews application telemetry in the Collabspace production environment to identify any issues, which are then fed back to Collabware’s Software Development team for review and resolution. A cloud-based SIEM (Security Information and Event Management) is also in place to offer systems analysis and actively monitor potential threats.
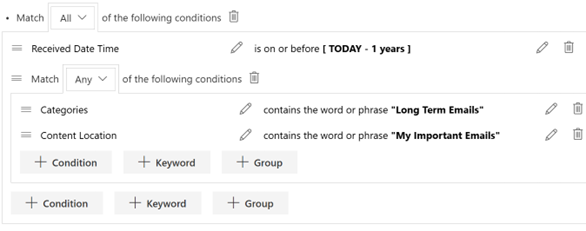
4. Capturing Multi-Repository Content and All Version Changes
Your selected cloud-based solution should properly store and safeguard content from the repositories you work in every day. As a data lake solution, Collabspace supports sourcing content from multiple Microsoft 365 services and from other on-premise sources such as network drives.
How? Collabspace streams in content from the on-premises or cloud-hosted content repositories using our agnostic and extensible Collabspace Content Connector Framework. Content is sourced through periodic crawling, real-time events, or a combination of the two approaches to ensure all content and applicable version changes are captured and stored in the secure Collabspace Content Storage System.
Once under management control of Collabspace, this content can be securely searched and accessed via multiple mediums and devices to meet legislative and regulatory requirements.
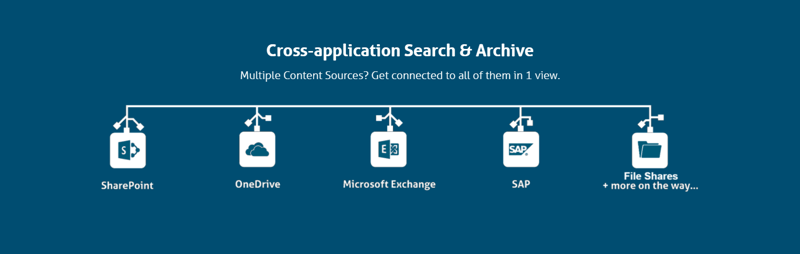
Collabspace streams in content from across SharePoint, OneDrive, Exchange, File Shares, and more.
5. Encrypting Content In-Transit and at Rest
For anyone questioning the security of streaming content: all information is encrypted both in transit and in storage with cryptographic HSM keys.
All Binary Large Object (BLOB) content sent to and from Collabspace is encrypted in transit using HTTPS with any modern browsers that support AES-128 or higher, such as Chrome, IE 11, Edge, and FireFox.”
For data at rest, BLOB content and associated BLOB properties stored in tenant repositories are individually encrypted used a rotating tenant-isolated key system managed by Microsoft Azure KeyVault. Collabware does not have access to the keys directly and has no ability to view encrypted content. Instead, each client-side decryption is required so Collabspace customer are assigned a separate KeyVault instance. Encryption keys and secrets are regularly rotated.
6. Storing Data in Multiple Jurisdictional Data Centers
Digital data is subject to laws of the country it resides, so it’s important to be mindful of where your organization’s data is stored.
All Collabspace data is stored in Microsoft Azure data centers, which are located geographically in the jurisdiction of our customers (currently either in Canada or the United States). Backups and copies for resiliency and/or availability are also stored in the same Azure jurisdiction as the customer data.
With multiple jurisdictional data centers, organizations adhere to regional data residency requirements and experience operational continuity with geo-replication.
7. Enhancing Protection Against Ransomware with WORM-Storage
Encryption keys, data centers, what’s next?
Collabspace has WORM-compliant storage, meaning that all data is stored as Write-Once-Read-Many (WORM) to ensure no data is overwritten or deleted. Making the content immutable after the initial write is critical to prevent any tampering or deletion so it is truly locked in. Only specific components have access to customer storage, as required for normal platform operations. WORM storage is also crucial to have so recovering data is quick and seamless in the event of accidental deletion or another incident.
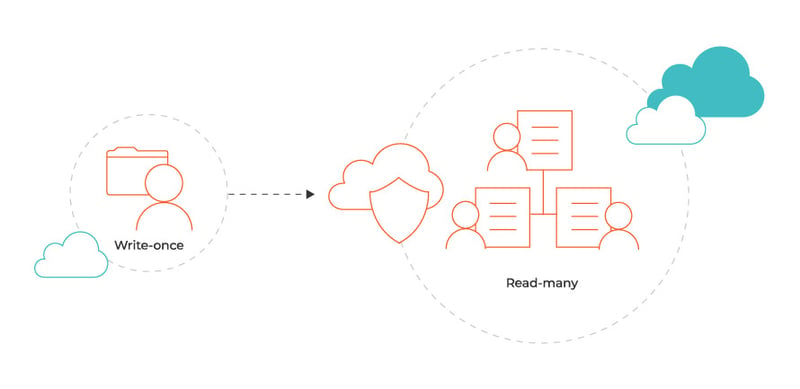 Diagram outlining WORM Compliance. Image courtesy of HubStor.
Diagram outlining WORM Compliance. Image courtesy of HubStor.
8. Requiring Authentication to Access Data
A big part of data privacy is making sure that only the right eyes view said data. With Collabspace, we take multiple steps to ensure that you can feel comfortable knowing that only those with permissions will view your content.
Collabspace fully integrates with the Azure Active Directory for all authentication and authorization controls. This integration allows Collabspace users to Leverage their own Azure Active Directory accounts to authenticate to Collabspace via the OAuth authentication protocol.
All application interfaces, communication and external interfaces require authentication, either via Azure Active Directory or mutual authorization-code or token-based authentication. Any non-secure or non-essential ports are disabled.
Collabspace does not create or store user credentials, instead these user accounts are created, managed and secured in Azure Active Directory by the consuming organization so only those with permissions in the organization will see.
9. Setting User Permissions and Privileged Identities
While Collabspace fully integrates with Azure Active Directory for authentication and authorization controls, Collabspace enables role-based access permissions for an additional layer of security clearance. All user permissions are managed through the Collabspace Administration app by the specified Organization administrators and applied to the relevant Azure Active Directory identities. Once a user is logged in, an access token is issued to define the login session and the token expires every two hours.
So who has access, exactly?
Whoever your organization has assigned
Client-side admin is performed by the administrators of the Collabspace tenant, who are responsible for adding the relevant users and assigning their permissions accordingly. Each tenant can only administrate their own security and permissions within Collabspace.
Limited views by Collabware DevOps for support operations
Only privileged identities (senior Collabware DevOps managers) have full access to the production environment, and only a few can monitor the environment and perform limited support operations… no other Collabware resources have access to the environment.
The Collabware Product Operations team can access application data related to the operation of Collabspace for a customer, but this does not include actual document content or metadata. All other customer data is encrypted and inaccessible to Collabware staff.
Collabware does not collect any personal information about customer employees for Collabspace.
10. Event Logging
To better manage security, performance and troubleshoot potential issues, event logging within Collabspace cannot be turned off and tracks numerous activities, including:
- Authentication
- Component Startup and Shutdown
- Any changes to component configuration
And each log message for each component contains the following elements:
- Event date and time
- Event description
- Account ID (User, device)
- End result (Success/Fail)
- Error ID if available
Operational security within Collabspace is controlled by Azure Active Directory, not a Collabware user login. Collabware users cannot access Collabspace operational systems unless they have authorization directly via the Collabspace AD.
11. Catching Potential Vulnerabilities and Backup in Case of Disaster
Firstly, Collabspace uses Azure platform security and audit alerting to identify potential security-related vulnerabilities and issues before they snowball into challenges. Input is reviewed by the Collabware Product Operations team to assess risk and criticality, and prioritize remediation. This alert information is available via a public status page to inform Collabspace end-users of performance degradation and functional issues, if relevant.
Secondly, in the very worst-case scenario, we have backup for data continuity. While highly unlikely, we want to prepare for any outcome. This is why all components within the Collabspace platform are continually replicated to a secondary datacenter to ensure continuity of service in case of an issue in the primary datacenter by either natural or human-caused disaster. This method employs multi-level redundancies to provide high availability and disaster recovery capabilities.
Failover to the secondary instances is automated, where possible. If not, alerts are configured to warn the Collabware Product Operations team and enable them to conduct a manual failover.
12. Training and Staying Updated on Current Information Security Policies
You can rest easy knowing that the team working on your cloud-based data repository is well versed in security. Collabware has achieved Service Organization Control (SOC)2, Type 2 Security and Availability Compliance audit. This audit tested and validated the controls we have in place to manage and secure data in the cloud for complete protection of our customers’ privacy.
As part of this compliance audit, Collabware demonstrated numerous control activities pertaining to the following areas:
- Staff education sessions on incident management and breach management
- Code of Conduct where staff must adhere to proper security measures
- Proving network and operating system security measures, including Azure AD authorization for access
- Third party penetration testing to ensure system security and integrity
- … and more! Email us if you are interested in a copy of the 25-page SOC2 Report for Collabware.
We know that stringent data privacy is not optional, it should be a given anywhere your organizational information is stored.
From security-minded solution development through to encryption and event logging, we’ve covered some of the careful steps taken so Collabspace protects your organizational data and ensures only authorized members have access.
Do you have any more questions around how Collabspace keeps your data safe? Download our free brochure outlining our security features, below. Check out the Collabware blog for more security-related articles, such as an overview of WORM-compliance, or checklists on how to remain compliant with your information archive, discovery and management. For more in-depth details, diagrams and background on our security protocols, please contact us with your questions!