Most organizations believe they are prepared for an audit. Data is stored in secure systems, policies exist, and platforms are in place to manage information. But when the conversation begins, the focus quickly shifts away from where the data lives and toward something much more critical:
What actually happened to it:
- How was it classified?
- Who accessed it?
- What decisions were made, and why?
This is where the difference between stored and governed becomes impossible to ignore.
Stored Vs Governed: The Real Difference
Stored data simply means that information exists in a secure location. It can be retrieved, it is protected, and it is technically managed. But governance goes far beyond that. Governed data tells a complete and defensible story. It shows:
-
How was information classified?
-
What policies were applied?
-
Who accessed it?
-
What actions were taken?
-
Why were those decisions made?
An auditor is not evaluating your infrastructure; they are evaluating your control over information. And control can only be demonstrated through evidence.
.png?width=367&height=307&name=Blog%20IQBG+%20Collabware%20(1).png) They want to understand how a record was handled from the moment it was created to its current state. If answering those questions requires manual reconstruction, pulling data from multiple disconnected systems, or relying on assumptions, then the issue is not a lack of storage; it is a lack of governance. In that moment, the gap becomes visible.
They want to understand how a record was handled from the moment it was created to its current state. If answering those questions requires manual reconstruction, pulling data from multiple disconnected systems, or relying on assumptions, then the issue is not a lack of storage; it is a lack of governance. In that moment, the gap becomes visible.
This confusion between storage and governance has created a false sense of security across many organizations. The presence of secure infrastructure and documented policies often leads teams to believe they are compliant. However, without consistent enforcement, visibility, and traceability, those policies may not actually be applied in practice.
Data may be over-retained, increasing legal exposure, or deleted too early, creating compliance risks. Access may not be properly tracked, and decisions may not be documented in a way that can be defended. When an audit occurs, these gaps are no longer theoretical; they become operational risks.
What Defensible Governance Actually Looks Like
Defensible governance is not a policy document. It’s not a set of guidelines stored in a shared folder. Is a system of continuous, provable control over information that ensures that every record, across every system, can answer a simple question: Can you prove what happened to this data - at any point in its lifecycle? The core component of defensible governance is automated, consistent, and auditable by design.
-
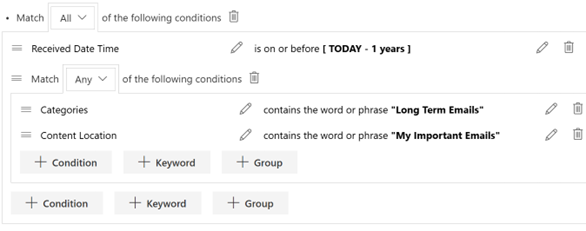
Automated Classification
According to the National Institute of Standards and Technology, effective data governance requires consistent classification frameworks to ensure data can be properly managed, secured, and audited across its lifecycle.
The categorization is based on predefined policies, not human discretion. The automation helps to reduce human error and ensure consistency across systems, and aligns data with regulatory requirements.
-
Policy-Driven Retention and Disposition
The retention schedule emphasizes that defensible disposition requires documented, repeatable processes that can be verified during audits, not just policies on paper.
These schedules are not just defined and enforced automatically, based on policies. Records are retained for the correct period, disposition actions are executed systematically, and every action is documented and traceable
-
Defensible Evidence on Demand
At any moment, an organization should be able to reconstruct the full lifecycle of a record (from creation to disposition), demonstrate how policies were applied, and generate audit-ready reports without delay. This capability eliminates the need for manual reconstruction, fragmented data collection, or reliance on assumptions.
Leading standards reinforce this expectation. The National Institute of Standards and Technology highlights the importance of auditability, traceability, and continuous monitoring as core principles of effective information governance, ensuring that all actions on data can be verified at any time.
The International Organization for Standardization (ISO 15489) emphasizes that records must be managed in a way that preserves reliability, integrity, and usability throughout their lifecycle, with evidence that can be produced when required.
Knowing the difference between stored and governed data is only the first step. The real question is whether your processes are truly audit-ready. Use the following checklist to assess your current state:
![]() You can identify ownership of any record instantly
You can identify ownership of any record instantly
![]() You can show how data was classified- automatically and consistently
You can show how data was classified- automatically and consistently
![]() You can demonstrate that retention policies are actively enforced (not just documented)
You can demonstrate that retention policies are actively enforced (not just documented)
![]() You have a complete, end-to-end audit trail of all actions taken on data
You have a complete, end-to-end audit trail of all actions taken on data
Most organizations fall somewhere in betwee theses questions. May organization have infrastructure and policies, but they lack the continuous, provable control required to demonstrate governance. And that gap only becomes visible when it matters most- during an audit.
So the final question isn’t: Is your data stored? It’s: Can you defend it?